As we kick off this year’s Reverse Engineering Survey (don’t forget to submit before October 7 to be eligible for the prizes), we wanted to spend some time digging into last year’s results and showing some of what we learned. And surprisingly, that includes the question of exactly how humble are reverse engineers! In total, our 2020 survey had 582 responses, of which 52% were Binary Ninja users. That’s not surprising since people likely to hear about the survey are necessarily more likely to already be Binary Ninja users.
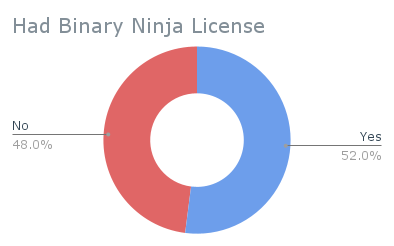
Given that, this is definitely a biased sample of the total set of reverse engineers so make sure to take that in mind when considering the results.
Respondents
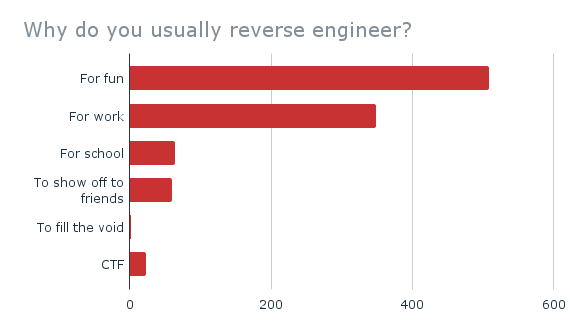
Motivation: Why do people reverse engineer?
As Vector 35 employees have a long history with playing CTFs (and many DEFCON black badges to prove it ;) ). We also think CTF players are probably over represented among respondents as Binary Ninja has a very steep discount for students. The respondents say they reverse engineer mainly for fun, and yet, over half also do it for work. Make sure to take breaks, it’s dangerous when your hobby is also your job!
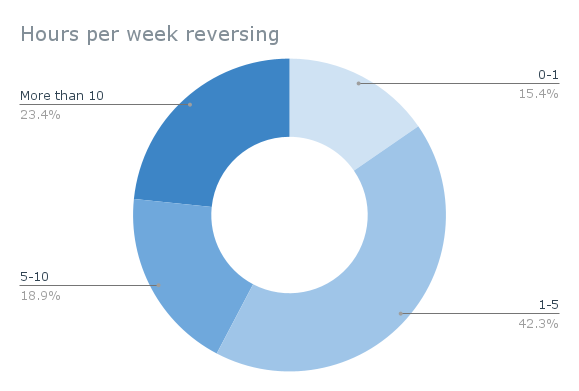
Frequency: How often do respondents reverse engineer?
Over half of respondents reverse engineer less than 5 hours per week.
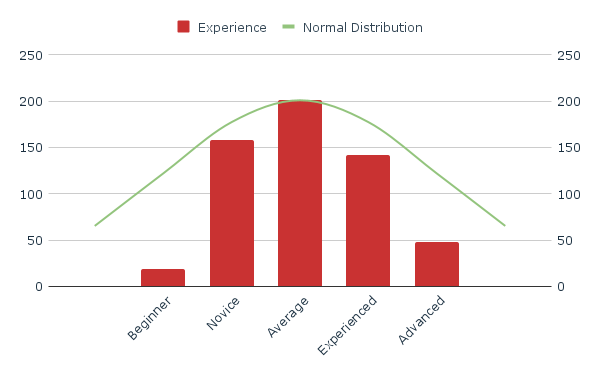
Reverse Engineers are… humble?
Most people believe they are above average. How about reverse engineers? Though the results skew slightly high, for the most part it seems to be a normal distribution. Maybe had we asked how good of a reverse engineer they are on a scale of 1-10 we’d have different results, or maybe not. Reverse Engineers could actually just be a humble group!
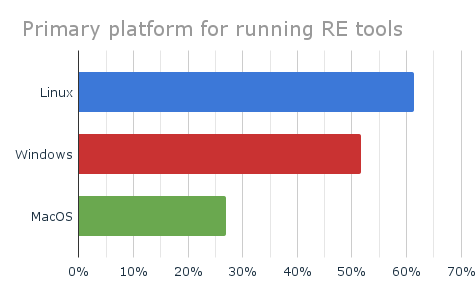
What OS are you running your tools on?
Not surprising that most people like to do reverse engineering on a Linux machine.
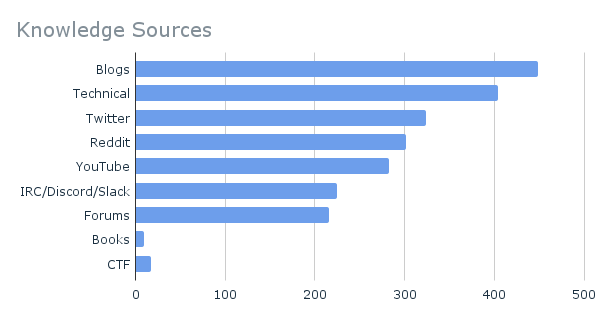
Where do you find out new information about reverse engineering?
It’s interesting to see where other get their knowledge from. We were surprised that people seem to get a lot of their knowledge from Twitter. Who knew it could be used for more than extolling the virtues of your favorite programming language?
Targets
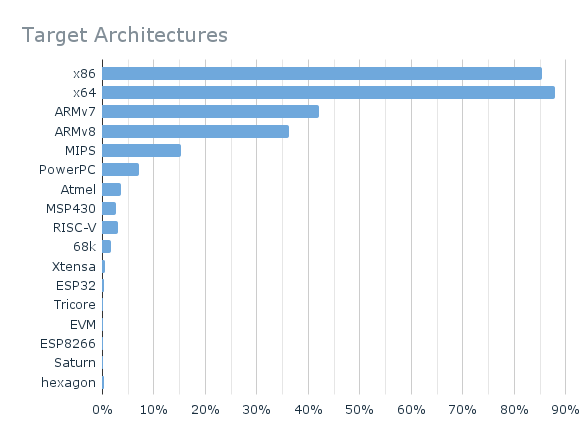
What architectures are you Reversing?
It’s not really a surprise that reverse engineering desktop/server architectures is the most common, followed by mobile, and then embedded. This probably reflects the abundance of CTF players.
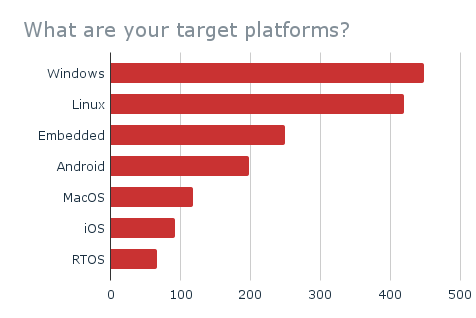
What platforms are you Reversing?
Windows is the top target platform among users, with Linux coming in second place. Two thoughts here. Windows has the worst malware problem, and Linux has the most CTF challenges. So these results aren’t surprising. It would be interesting to see how these trends change when controlled for different subsets of respondents.
2021 Survey is LIVE!
This year we’ve improved our survey with more questions and plan on doing an even more thorough analysis of the data. We want to be able to answer questions like:
- Do experienced reverse engineers spend their RE time differently than beginners?
- How do most people spend their time while reverse engineering?
- How does time spent reverse engineering correlate to perceived experience?
- What are the differences among people doing vulnerability research vs malware analysis?
If you’re a reverse engineer we’d love your input. The survey only takes about 5 minutes to complete and there are even prizes!